Cybersecurity: 24/7/365
Cybersecurity: 24/7/365
Your office manager gets a call from someone claiming to be your EHR vendor's support team. They reference your practice by name, mention the software version you run, and explain that a critical security patch requires remote access to your server. The caller sounds professional, knowledgeable, and urgent. Your office manager grants access. Within 30 minutes, an attacker has installed remote access tools on three workstations and is downloading your patient database.
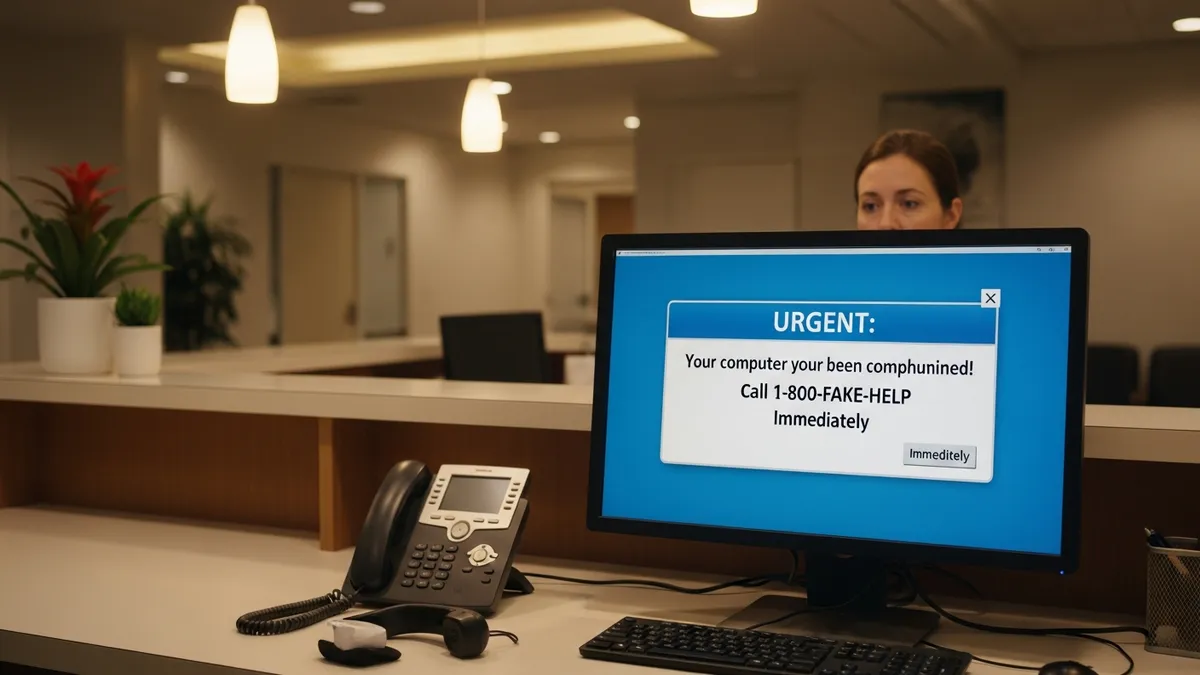
No malware was involved. No firewall was bypassed. No password was cracked. The attacker simply asked — and your staff said yes. That is social engineering.
Social engineering is the manipulation of people into giving up confidential information or access. It is the number one attack method in healthcare, responsible for 45% of all healthcare data breaches. And it is getting worse: AI-driven social engineering attacks have increased 1,265% since 2023, with AI-generated phishing emails achieving 42% higher click rates than human-written ones.
Medical records sell for $250 to $1,000 each on the dark web — 10 to 50 times the value of a credit card number. A single patient record contains names, dates of birth, Social Security numbers, insurance details, and medical histories. Unlike a credit card, this data cannot be canceled or reissued. It is useful to criminals for years.
Small medical practices are targeted at roughly 4 times the rate of large enterprises. Attackers know that practices with 1 to 50 employees typically have:
In 2024, 92% of healthcare organizations experienced a cyberattack. 55.8% of ransomware attacks targeted companies with fewer than 50 employees. The median time to fall for a phishing email is under 60 seconds — 21 seconds to click a malicious link and 28 seconds to enter credentials on a fake page.
1. Pretexting — the fastest-growing tactic. An attacker fabricates a detailed scenario to extract information or access. They might pose as an IT auditor, a compliance inspector, a DEA agent, or a new insurance representative. In October 2024, the DEA issued a formal alert about scammers impersonating DEA agents, threatening doctors with arrest and license revocation while referencing their real NPI numbers and state license numbers. Pretexting now accounts for over 50% of all social engineering attacks — double the rate from the previous year.
2. Phishing — the volume play. Mass emails impersonating trusted entities — EHR vendors, insurance companies, government agencies. Subject lines create urgency: "Your HIPAA certification expires tomorrow" or "Patient complaint requires immediate response." In 2024, 180 healthcare organizations fell victim to email-related breaches. Phishing training is the most effective defense.
3. Vishing — voice phishing. Phone calls impersonating IT support, software vendors, or government agencies. Vishing attacks surged 442% in 2024. In April 2024, HHS issued an alert about attackers calling healthcare IT help desks using stolen employee identities, correctly answering security questions, and requesting password resets and new MFA device enrollment. AI voice cloning makes these calls nearly indistinguishable from legitimate callers.
4. Business email compromise (BEC). The attacker compromises or impersonates a real email account — often the practice owner or office manager. They instruct billing staff to redirect wire transfers or change payment information. BEC attacks caused $2.77 billion in losses in 2024, with a median loss of $50,000 per incident. A single BEC email can bankrupt a small practice.
5. Baiting. Physical or digital lures. Leaving malware-infected USB drives in break rooms or parking lots. Sending fake software updates disguised as legitimate vendor patches. The Zeon threat group targeted 35,000 healthcare email addresses impersonating healthcare software vendors, tricking victims into installing remote access tools.
6. Tailgating. Following authorized personnel through secure doors. Posing as delivery drivers, pharmaceutical reps, HVAC technicians, or copier repair workers to gain physical access to areas containing workstations, servers, or paper records. Once inside, attackers can access unlocked computers, photograph screens, or plug in rogue devices.
Change Healthcare (February 2024). An attacker used stolen credentials from a low-level customer support employee to access a system that lacked multi-factor authentication. Over 9 days, the attacker moved through the network before deploying ransomware. Result: 192.7 million patient records exposed, $2.457 billion in total costs, and $22 million in ransom payments. 80% of physician practices lost revenue from unpaid claims. A single compromised credential without MFA caused the largest healthcare breach in U.S. history.
HC3 IT Help Desk Attacks (April 2024). Attackers called healthcare IT help desks using stolen identities of revenue cycle employees. They correctly answered security questions — including the last four digits of Social Security numbers and corporate ID numbers — then requested password resets and new MFA device enrollment. At least two successful attacks diverted legitimate payments to attacker-controlled bank accounts.
DEA Impersonation Campaign (October 2024). Nationwide vishing campaign targeting doctors and pharmacists across all 50 states. Scammers impersonated DEA agents, referenced real NPI numbers, threatened arrest and license revocation, and demanded wire transfer "fines." The calls exploited the high-pressure environment of medical practice to bypass rational thinking.
Scattered Spider (2024-2025). An English-speaking threat group (ages 19-22) from the U.S. and UK used social engineering and AI voice spoofing to target healthcare organizations. They enrolled in MFA on compromised accounts and deployed RansomHub and Qilin ransomware specifically targeting healthcare.
Verification protocols. Establish a "trust but verify" culture for every request involving access, credentials, or money:
Staff training — the human firewall. Your staff is either your biggest vulnerability or your strongest defense. The difference is training.
Technical controls. Layer technology behind your human defenses:
Physical security. Social engineering is not just digital:
A social engineering attack that exposes PHI is a reportable breach under HIPAA. But even without a breach, failure to train staff on social engineering recognition is itself a HIPAA violation under §164.308(a)(5), which requires a security awareness and training program for all workforce members.
The proposed 2026 HIPAA Security Rule update would make annual security awareness training mandatory with specific topic requirements — including social engineering. Practices that already train their staff will be ahead. Practices that do not will face both regulatory pressure and increased attack risk.
Penalties for HIPAA violations range from $145 to $2.19 million per violation category. Lafourche Medical Group paid $480,000 after a phishing attack — and OCR cited the lack of security awareness training as a primary finding. The average cost of a healthcare data breach is $10.22 million. The average time to identify and contain a social engineering breach is 257 days.
Social engineering attacks do not break through your firewall. They walk through the front door because someone held it open. The attacks are getting more sophisticated — AI voice cloning, deepfake video, and spear phishing that references your real vendors, real patients, and real processes.
The defense is straightforward: train your staff, verify every request, and layer technical controls behind your human firewall. A managed IT provider that includes security awareness training, phishing simulations, and 24/7 monitoring makes this manageable for a small practice.
60% of small businesses close within 6 months of a major breach. Do not let a single phone call or email be the reason your practice becomes a statistic.
Book a free IT assessment to evaluate your practice's social engineering defenses. We will run a baseline phishing test, assess your verification protocols, and build a training program that turns your staff into your strongest security layer. Explore our cybersecurity services and managed IT plans.